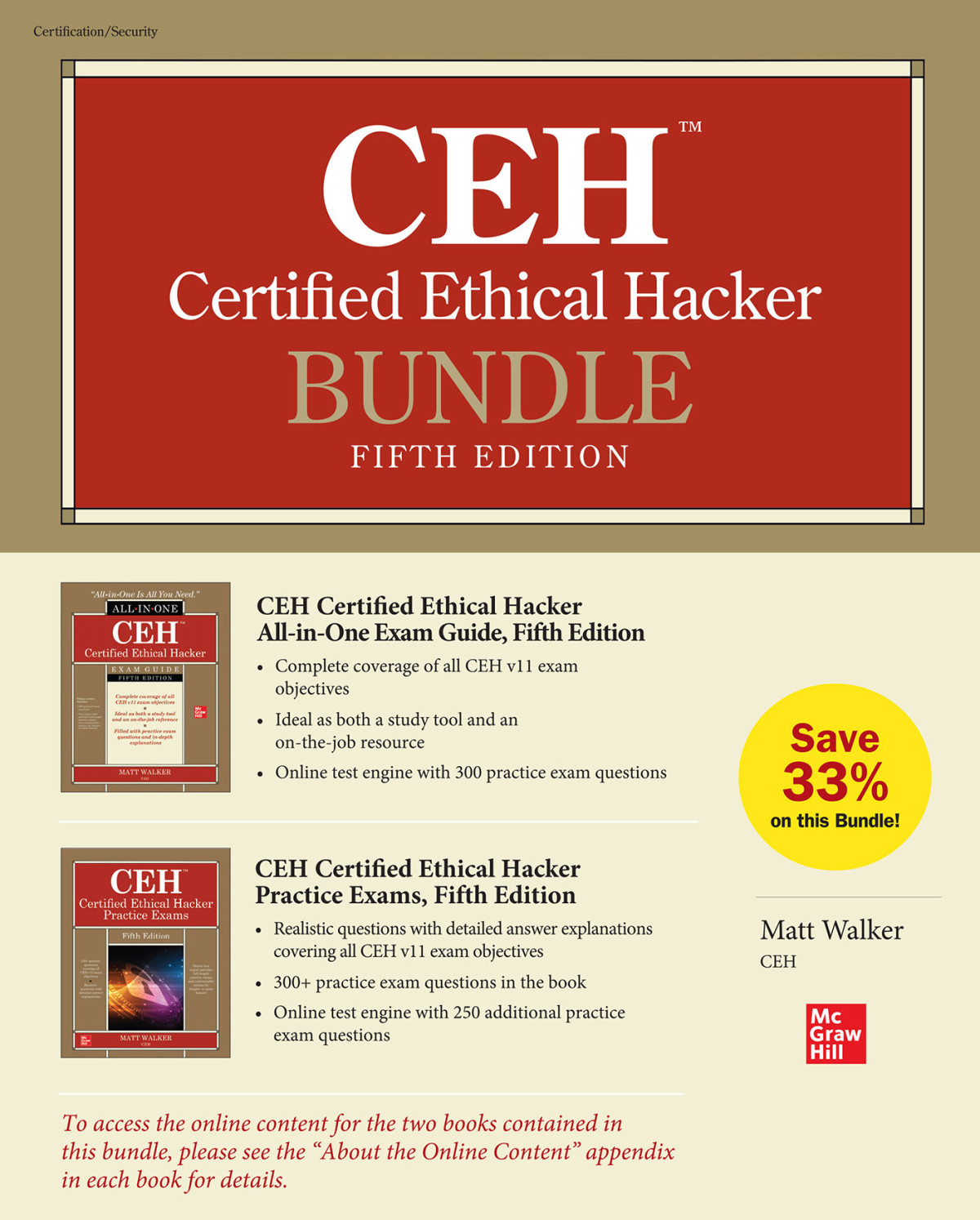
CEH Certified Ethical Hacker Bundle 5th Edition by Matt Walker 1264269952 9781264269952
$50.00 Original price was: $50.00.$25.00Current price is: $25.00.
CEH Certified Ethical Hacker Bundle 5th Edition by Matt Walker – Ebook PDF Instant Download/DeliveryISBN: 1264269952, 9781264269952
Full download CEH Certified Ethical Hacker Bundle 5th Edition after payment.
Product details:
ISBN-10 : 1264269952
ISBN-13 : 9781264269952
Author: Matt Walker
Up-to-date coverage of every topic on the CEH v11 exam Thoroughly updated for CEH v11 exam objectives, this integrated self-study system offers complete coverage of the EC-Council’s Certified Ethical Hacker exam. In this new edition, IT security expert Matt Walker discusses the latest tools, techniques, and exploits relevant to the exam. You’ll find learning objectives at the beginning of each chapter, exam tips, practice exam questions, and in-depth explanations. Designed to help you pass the exam with ease, this comprehensive resource also serves as an essential on-the-job reference. Covers all exam topics, including: Ethical hacking fundamentals Reconnaissance and footprinting Scanning and enumeration Sniffing and evasion Attacking a system Hacking web servers and applications Wireless network hacking Mobile, IoT, and OT Security in cloud computing Trojans and other attacks, including malware analysis Cryptography Social engineering and physical security Penetration testing Online content includes: 300 practice exam questions Test engine that provides full-length practice exams and customized quizzes by chapter or exam domain
CEH Certified Ethical Hacker Bundle 5th Table of contents:
Chapter 1 Getting Started: Essential Knowledge
Security 101
Essentials
Security Basics
Introduction to Ethical Hacking
Hacking Terminology
The Ethical Hacker
Chapter Review
Questions
Answers
Chapter 2 Reconnaissance: Information Gathering for the Ethical Hacker
Footprinting
Passive Footprinting
Active Footprinting
Footprinting Methods and Tools
Search Engines
Website and E-mail Footprinting
DNS Footprinting
Network Footprinting
Other Tools
Chapter Review
Questions
Answers
Chapter 3 Scanning and Enumeration
Fundamentals
TCP/IP Networking
Subnetting
Scanning Methodology
Identifying Targets
Port Scanning
Evasion
Vulnerability Scanning
Enumeration
Windows System Basics
Unix/Linux System Basics
Enumeration Techniques
Chapter Review
Questions
Answers
Chapter 4 Sniffing and Evasion
Essentials
Network Knowledge for Sniffing
Active and Passive Sniffing
Sniffing Tools and Techniques
Techniques
Tools
Evasion
Devices Aligned Against You
Evasion Techniques
Chapter Review
Questions
Answers
Chapter 5 Attacking a System
Getting Started
Windows Security Architecture
Linux Security Architecture
Methodology
Hacking Steps
Authentication and Passwords
Privilege Escalation and Executing Applications
Hiding Files and Covering Tracks
Chapter Review
Questions
Answers
Chapter 6 Web-Based Hacking: Servers and Applications
Web Servers
Nonprofit Organizations Promoting Web Security
Attack Methodology
Web Server Architecture
Web Server Attacks
Attacking Web Applications
Application Attacks
Countermeasures
Chapter Review
Questions
Answers
Chapter 7 Wireless Network Hacking
Wireless Networking
Wireless Terminology, Architecture, and Standards
Wireless Hacking
Chapter Review
Questions
Answers
Chapter 8 Mobile Communications and the IoT
The Mobile World
Mobile Vulnerabilities and Risks
Mobile Platforms and Attacks
IoT
IoT Architecture
IoT Vulnerabilities and Attacks
IoT Hacking Methodology
OT Hacking
Definition and Concepts
Security Concerns
Chapter Review
Questions
Answers
Chapter 9 Security in Cloud Computing
Cloud Computing
Cloud Computing Service Types
Cloud Deployment Models
Cloud Security
Cloud Threats
Cloud Attacks and Mitigations
Cloud Hacking
Chapter Review
Questions
Answers
Chapter 10 Trojans and Other Attacks
The “Malware” Attacks
Trojans
Viruses and Worms
Fileless Malware
Malware Analysis
Malware Countermeasures
Remaining Attacks
Denial of Service
Session Hijacking
Chapter Review
Questions
Answers
Chapter 11 Cryptography 101
Cryptography and Encryption Overview
Terminology
Encryption Algorithms and Techniques
PKI, the Digital Certificate, and Digital Signatures
The PKI System
Digital Certificates
Digital Signatures
To Sum Up
Encrypted Communication and Cryptography Attacks
Encrypted Communication
Cryptography Attacks
Chapter Review
Questions
Answers
Chapter 12 Low Tech: Social Engineering and Physical Security
Social Engineering
Human-Based Social Engineering Attacks
Computer-Based Attacks
Mobile-Based Attacks
Preventing Social Engineering Attacks
Physical Security
Physical Security 101
Testing Physical Security
Chapter Review
Questions
Answers
Chapter 13 The Pen Test: Putting It All Together
Methodology and Steps
Security Assessments
Security Assessment Deliverables
Guidelines
More Terminology
Chapter Review
Questions
Answers
Appendix A Tool, Sites, and References
Vulnerability Research Sites
Footprinting Tools
Scanning and Enumeration Tools
System Hacking Tools
Cryptography and Encryption
Sniffing
Wireless
Mobile and IoT
Trojans and Malware
Web Attacks
Miscellaneous
Tools, Sites, and References Disclaimer
Appendix B About the Online Content
System Requirements
Your Total Seminars Training Hub Account
Privacy Notice
Single User License Terms and Conditions
TotalTester Online
Technical Support
People also search for CEH Certified Ethical Hacker Bundle 5th:
what is certified ethical hacker (ceh)
certified ethical hacker (ceh) price
certified ethical hacker (ceh) requirements
how to become a ceh certified ethical hacker
certified ethical hacker cost
Tags: CEH Certified, Ethical Hacker, Matt Walker, Bundle
You may also like…
Computers - Computer Certification & Training
CEH Certified Ethical Hacker Practice Exams, 5th Edition by Matt Walker 1264269978 9781264269976
Computers - Security
The Pentester BluePrint: Starting a Career as an Ethical Hacker 1st Edition Phillip L. Wylie
Computers - Computer Certification & Training
Computers - Computer Certification & Training
CEH All-in-One Exam Guide 3rd Edition Professional Matt Walker
Computers - Computer Certification & Training
Computers - Networking
CISA Certified Information Systems Auditor Bundle 1st Edition Peter H. Gregory
Computers - Internet & World Wide Web
CEH Certified Ethical Hacker All-in-One Exam Guide 5th Edition Walker
Computers - Internet & World Wide Web
CEH Certified Ethical Hacker All-in-One Exam Guide, 5th Edition Matt Walker